How to Use FIDO Authentication to Secure IoT Devices?

What is FIDO (Fast Identity Online) ?
FIDO (Fast Identity Online) literally means it’s a method related to online identification. There have been increasing problems in password verification in traditional IT systems, including account being hacked, unfriendly user experience, hard-to-remember password, and so on. Meanwhile, the more secure and faster internet identity verification technologies for internet connection are required. Consequently, numbers of well-known companies, such as PayPal, Nok Nok Labs, Lenovo, established FIDO Alliance in 2012 to build FIDO standards. In recent years, more technology companies have joined the alliance, like Google, Alibaba, Intel, Qualcomm, and even Visa, American Express. These companies are all dedicated to promoting the password-less, safe, and easy way for online authentication to solve the identification problems in any public or private cloud.
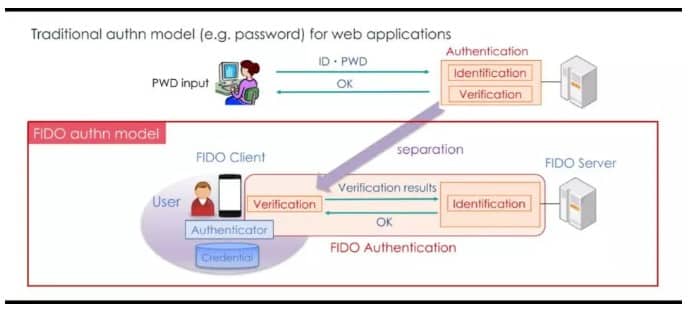
Like the picture above, FIDO authentication model is composed of local authentication device and remote server device. Different from password authentication in traditional internet services, FIDO authentication does not transmit password via internet but separates Verification and Identification. Users need to use an Authenticator at local end, like smart phone, USB Key, smart card, secure device to store personal identity authentication data, and also apply Public Key Infrastructure to transmit the verification results. According to the results, the server, at remote side, will check if the access request is eligible. The key features of this method include:
1. There’s no password and private key stored in server side, so there’s no personal privacy issue. Even if the server is hacked, it won’t cause individual data breach.
2. FIDO protocol aims to build the open standards of identification without password, so it combines biometric authentication, second-factor authentication, and multi-factors authentication to realize FIDO.
M2351 USB FIDO Key Reference Design
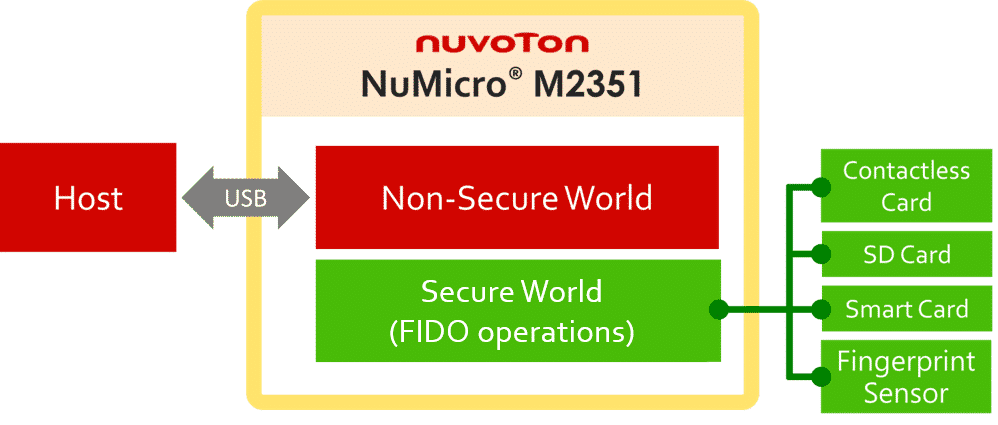
Based on the description mentioned above, let’s see Nuvoton’s reference design, Smart Authentication—USB FIDO Key:
M2351 is based on Armv8-M TrustZone® infrastructure, so we suggest you store the authentication-related codes in Secure World, such as connecting Fingerprint Sensor, Smart Card, Micro SD, or the interface for wireless transmission to read NFC card. As to the non-authentication-related codes, you could store in Non-Secure World, for example, transmitting data or supplying power from USB interface to PC/Notebook. The advantages of using this solution include:
• It is the best platform for FIDO end product with multiple functions and security. For example, the traditional access control in a company could be the ID card, and the way to verify the website access is controlled by USB Dongle/ U-Key. However, the ID card could be stolen, and users need to input passwords with U-Key. So, the integrated device can make the office resource access more easily and secure.
• It’s a reference design with compatible price. Traditional general-purpose microcontrollers are not equipped with TrustZone and do not fully support data encryption, even not to mention software IP protection. Traditional MCUs are designed for Smart Card so that the peripheral support and computing capabilities are limited. That’s why multi-factor authentication (password-less) cannot be realized. Combining TrustZone and XOM (eXecute-Only-Memory), M2351 is the only microcontroller that implements the software IP protection. Within some private cloud, designers even do not need add secure elements. If you’d like to apply the MCU to smart card level, you may apply ISO-7816 to read smart card, SD card, Security IC Secure Element. Meanwhile, M2351’s high performance and low power features enable faster fingerprint sensor identification function.
• It’s a platform suitable for secondary development. Not all companies have the expertise on cyber security and peripheral sensing. Through the platform, the companies with better techniques are able to concentrate on developing the core FIDO development kit. Meanwhile, the companies who either have sales channels or end product manufacturing demand could develop the software design, product design and manufacturing. With this cooperation, not only is the core software security protected, but also the FIDO end products could be applied commonly.
M2351 USB FIDO Key: Secondary Development Security Level
As to the security level, it is believed that FIDO applications can be diverse, and there will be more and more types of FIDO authentication devices released to the market. So the high level storage security of personal identification certificate will be required. If the certificate includes biometric authentication, such as fingerprint, the fingerprint data should be stored in a secure area. So we need to remind readers that you can enhance the security by connecting Smart Card (e.g. SIM card), SD Card, Security IC (Secure Element), etc. To meet the fast and high security requirement, NuMicro M2351 will be the best MCU to work with SIM card, SD card, and security IC.
Shop NuMicro M2351 microcontrollers and Development Board now!
(The original version is from “M2351应用系列:智能认证 (Smart Authentication)” by Li-Min Ling, Technology Manager at Nuvoton Technology Corp.)
Sign up to become TechDesign member and get the first-hand supply chain news.